info@oxtrabot.com
855-750-0004

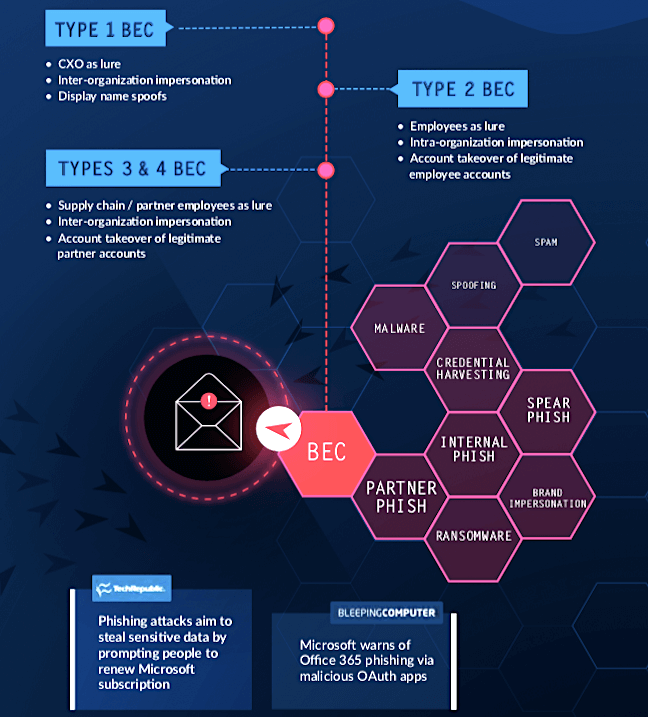
Business email compromise is out of control and one of the biggest risks!
Area 1 knows how to mitigate these risks to avoid incidents. Install only takes 25 minutes with Office 365 accounts!
Oxtrabot is offering a free email assessment to identify phishing threat vectors.
How can we help you?
What is email authentication?
Any time email fraud is mentioned, email authentication (specifically, SPF, DKIM and/or DMARC) is almost always brought up as the answer. While email authentication can protect against some forms of fraud and spoofing, it is largely ineffective against the most common and dangerous type of email fraud — phishing.
Stopping email fraud and sophisticated phishing attacks, especially those relying on social engineering, require advanced detection techniques.
Email authentication typically refers to any one of three common email authentication standards that verifies the origin of an email and who it claims to be from: SPF, DKIM and DMARC. These standards serve useful security functions such as validating server and tenant origins, protecting message integrity and providing policy enforcement.
All three standards can help with preventing some forms of phishing, but attackers can easily circumvent email authentication.
Recent ongoing research has exposed at least 18 techniques to trick email authentication into thinking an email from an attacker’s server is verified as coming from a legitimate address.
Why is email authentication ineffective with phishing attacks?
Email authentication does not protect against compromised domains. Email authentication does not protect against legitimate domains that have been compromised. Many phishing attacks come from compromised Office 365 accounts, and compromised tenants can also host phishing sites or malware.
This also means email authentication is ineffective against Business Email Compromise (BEC) attacks, particularly Types 3 and 4 BEC attacks, which leverage compromised partners and supply chain vendors to target phishing campaigns.
The vast majority of organizations and domains do not use email authentication. While email authentication cannot prevent all phishing and targeted attacks, it can still help — if it’s been configured.
Ask an expert at Oxtrabot, about our free assessment.
You have nothing to lose besides the Phish!

Questions? Call us toll-free 1-855-750-0004 or support@oxtrabot.com